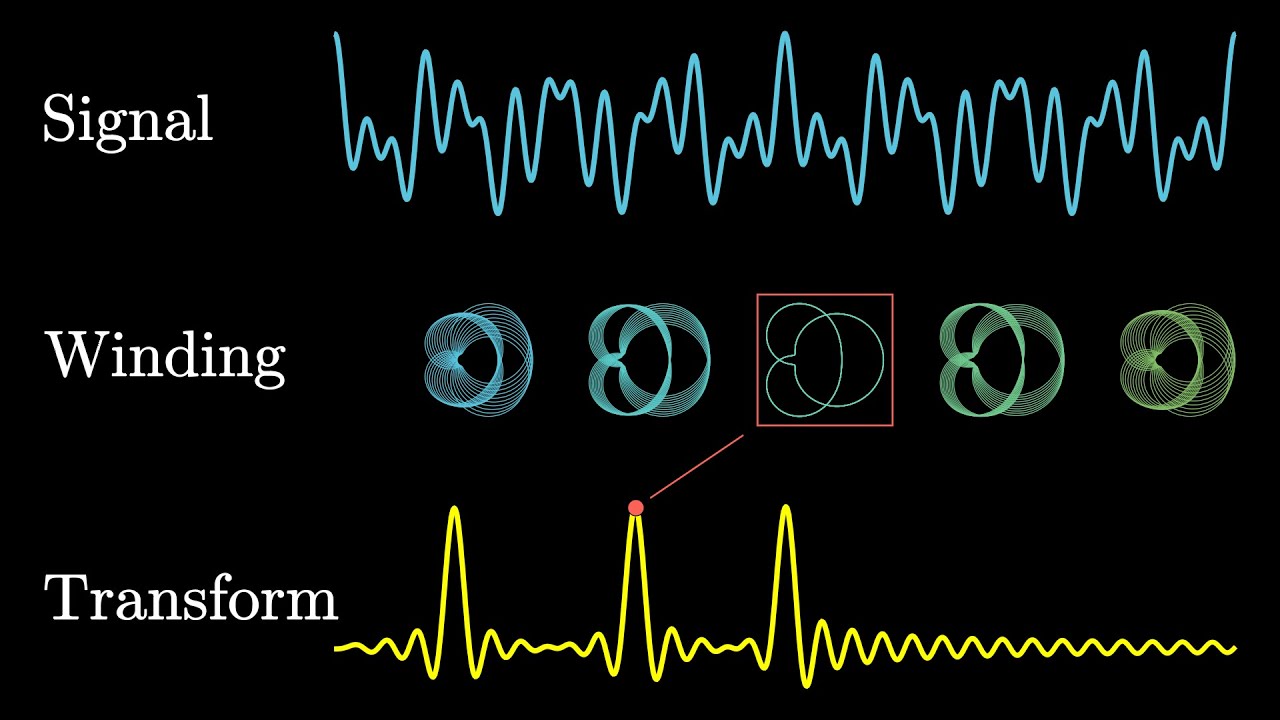
This is a simple Inverter Driver emulation which I produced to help me build a signal modulator for our P2P internet as well as distributed power. It can also be useful for someone who would like to build a driver for an inverter from scratch.
… and from this emulator I was able to produce a lot of code. It’s loosely organized for you, for now, and I intend to improve the organization later on.
This is based upon my pre-explainer videos:
and
and
AS WELL AS:
Without further wait, here is the rough draft for our rendition of DISTRIBUTED ISP, the portion of which I have been refining of late is our signal compression and propagation protocol:
Today I will add this file to our library, which is the combined result of most all the other files in the sub-folder. I will add an even better version later on…
This adds quadrilateral adjustment to our data mesh. The idea is a mutable shell of data, a mutable interweaving helix to construct the innards, and inter-relationship between the two to make ‘the whole greater than the sum of the parts.’ We are also beginning to add crude error correction, which is mostly placeholder at this time. The more complicated things get, the more collisions and the more difficult it is to integrate it all together. The nice thing is, Python is really good at wrapping functions together to make them mutually inclusive. I know our finished inverter modulation will be highly compressed and highly nimble, although part of the reason I am releasing this as open source is we will also need to transition our compute technique from binary (0, 1) to analog (0, 1, -1) and so anyone trying to copy this work without attribution will hit a real dead end (not enough computing resources) without my consult. Thanks.
This Proof of Non-Tamperability (PoNT) algorithm eliminates the ballooning ledger problem and improves anonymity by using a tamper-evident seal to verify the integrity of the transaction data. The seal is calculated by hashing the transaction data. The transaction data is encrypted using a shared key. The shared key is encrypted using the public keys of the receiving nodes. The encrypted transaction data and encrypted shared key are broadcasted to the receiving nodes. The receiving nodes decrypt the shared key using their private keys. The receiving nodes then decrypt the transaction data using the shared key. The receiving nodes verify the tamper-evident seal on the transaction data using the public key of the sender. The receiving nodes then add the transaction to their local blockchain - this part I will trim soon, as we don’t actually want our blockchain to store anything but PoNT, to prevent ballooning. ABI information will soon be stored only in the public / private keys, which are encoded themselves to include the ABI. The public key doesn’t exist unless called upon, eventually, for privacy while the ABI information will eventually be returned to the lineup and also will not exist unless called upon. The algorithm is intended to be soon ready for export via the radio.py module, enabling P2P radio ISP.
This code combines the PoNT.py code with the radio.py code to create a radio communication system that uses the PoNT algorithm to encode and decode the data in order to create a distributed ISP that is resistant to interference and can be used to communicate with other radio stations in the area.
The Filter.h modulates our inverter-as-amp to make the magic happen between a node and radio
For this version I’ve ditched some of the higher level logic, for now, in hopes of getting a product going soon. We can always make an improved V2.0 which restores some of the principles, and for now V0.2 is coming together nicely.
Add / trim, add / trim, add / time - We have trimmed some concepts which I will restore soon, and we have trimmed some concepts for good, and we have added some concepts which I will later refine by trimming. Rinse and repeat. This is a rough draft, of course it’s not complete.
Another less known means of achieving analog computing, in addition to the old school tubes, is modulation. The incandescent motor, for example, is simultaneously capable of logic and propagation of signal by means of modulating the revolving motor’s output signal. Every partial revolution performs our data transmission coupled with power generation, one unit to rule them all, and this can of course be stacked and even combined with other motors ad hoc. Static toroids can play the game too.
Speaking of ad hoc, mo motors means creating interesting optimizations physical and digital, digital ad hoc itself being rendered practical by encryption of our various signals, combined. As has been said, the whole is greater than the sum of the parts.
Liquid crystal dynamic circuit manifold membrane - can our flip chip be modular, as enabled by LCD-esque tech? An aside.
No no no! Long range ground-to-ground for health, air to air for sickness, is it not so? Short range air-to-air for health per https://forum.chgcoin.org/t/rejuvinating-wifi-transformer-emf/